In the current digital world, the verification of user identity has become crucial for all parties involved: businesses, governmental institutions, and individual users. Online services would not be able to function without the ability to verify users for a myriad of reasons including safety and security of financial transactions. Among the various technologies that can help with the verification processes, the most advanced and user-friendly is verifiable credentials (VCs) which help users retain their privacy and control over their personal data.
What Are Verifiable Credentials?
Verifiable credentials can be defined as digital identity constructs containing personal information that can be verified (or authenticated) through the use of cryptography. This collection of personal information may include a user’s date of birth, a user’s professional credentials, a user’s various licenses, and a user’s memberships. Compared to conventional systems of identity verification, verifiable credentials empower users to manage their verified information and provide access as appropriate while limiting data disclosure.
For instance, instead of providing a complete driver’s license to the relevant parties to verify that a user is more than 18 years of age, a user can obtain a verifiable credential that electronically confirms the user’s age without noting how old the user is. This process not only confirms the user’s age, but it also protects user information.
How Using Verifiable Credentials Work
Three main players are involved in the verifiable credentials model:
- Issuer – Signs and prepares the verifiable credential.
- Holder – Person who receives the credential and keeps it in a digital wallet.
- Verifier – Stakeholder who needs evidence of the credential.
The credential’s issuer keeps it safe and digitally signs it. When a review is needed, the credential holder needs to show it to the verifier. The verifier can perform a rapid authenticity check through a digital signature.
The system also provides the ability to checkpoint credentials and perform identification and authentication once per system.
Private Identity and Verifiable Credentials
One of the organizations behind the development of this technology is Private Identity. This company was started in 2017, and is located in Washington, DC. The company develops technology to preserve the confidentiality of processes used in the verification of digital identities and employs biometric methods, cryptographic methods, and methods of implementing secure digital identities.
Private Identity develops technologies that enable organizations to develop and implement digital identities for users. These identities are based on verifiable credentials and can be issued, authenticated, and attributed via secure web wallets. Credentials can be issued, authenticated, and attributed via web wallets, and remote credential sharing is possible for authentication, onboarding, and attribute verification.
A central part of their method is privacy-first design. Processes like identity verification and biometric authentication can be done on the user’s device, meaning that no sensitive data, including photos or personally identifiable information, has to be sent to remote servers. This decreases potential security threats and enhances privacy risks.
Benefits of Using Verifiable Credentials
Verifiable credentials offer significant value compared to legacy identity systems.
- Data Protection and Privacy
Users have the ability to protect their personal data as less information is required to be disclosed to a verifier. This diminishes the likelihood of identity fraud and data misuse.
- Secure Data With Cryptography
The information presented is guaranteed to be accurate and uncompromised as the data is protected from any modifications and has been digitally signed.
- Digital Identity That is Reusable
The entire verification process does not need to be done again as a credential that has been activated can be used to access multiple services.
- Use of Different Platforms
Organizations can recognize credentials issued by their trusted providers, assuring security, as verifiable credentials are cross-compatible.
- Quicker User Integration and Authentication
Organizations can improve user sign up and authentication processes as well as authorization procedures with the use of trusted digital identities.
Use Cases
Multiple industries and use cases are beginning to implement verifiable credentials.
Financial Services
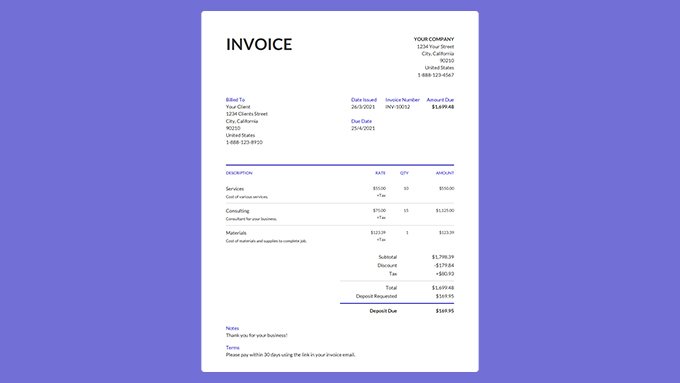
Banks, as well as fintech platforms, could uptick their customer facilitation efforts by enabling customers to use previously verified identity credentials at other banks to ease identity verification.
Workforce Identity
Employers can provide their employees and contractors with digital credentials to control their access to certain systems, places, and assets.
Education and Certifications
Educational institutions are able to provide employers with the ability to receive validated digital diplomas and certificates instantly.
Age Assurance
Online platforms can confirm if a user is of legal age to use their services without revealing their identity.
E-commerce and Payments
Identities that are verified and linked are able to speed up the verification to complete a transaction and, as a result, lower the occurrence of fraudulent transactions.
Private Identity Systems
Security and privacy are two opposing factors when it comes to managing digital identity systems. The more traditional identity systems store sensitive data of their users in a single database, which is then at risk of being compromised.
Today, the risk is lower by utilizing newer technologies to help users control their credentials and reduce the amount of sensitive data stored by an organization. These systems that use decentralized systems and crypto token verification are improving identity systems in a more secure and user-friendly way.
The Future of Digital Identity
Insecure digital interactions increase the demand for reliable identity verification systems. Next generation digital identity infrastructures may include verifiable credentials from all sectors of industries to enable secure and privacy-focused verification systems
The technology of Verifiable credentials helps organizations minimize time and identity fraud. Increased privacy for digital users through control, and protection of digital identities creates a a secure and user-centered digital ecosystem.