Introduction: When Passing the Scan Is No Longer Enough
Your DAST scan runs successfully. No critical issues are reported, and everything appears secure. But in reality, a user might still exploit a flaw in your application’s workflow, such as applying a discount multiple times or bypassing a required step.
This highlights a growing gap in application security. Traditional DAST tools were built to detect known technical vulnerabilities, not misuse of application logic. However, modern attacks increasingly focus on how applications behave rather than how they are coded.
As applications become more complex, with APIs, dynamic workflows, and multiple user roles, this gap becomes more visible. Security testing must now go beyond pattern detection and focus on how real users and attackers interact with the system.
What Traditional DAST Tools Were Designed To Do
Traditional Dynamic Application Security Testing works by interacting with a live application and identifying vulnerabilities based on known patterns. It sends requests, analyzes responses, and flags issues such as injection flaws or misconfigurations.
This approach has made DAST a reliable part of security programs. It is useful for identifying common vulnerabilities, works across different technologies, and integrates easily into CI/CD pipelines.
For known and repeatable issues, DAST provides consistent results and helps maintain baseline security across applications.
Where Traditional DAST Struggles in Modern Applications
As applications evolve, the limitations of DAST become more visible. Modern systems rely on complex authentication, dynamic frontends, and interconnected services, which are difficult to fully test using predefined scanning logic.
DAST evaluates requests individually and does not track how actions connect across a workflow. This means it cannot detect issues that only appear when multiple steps are combined.
Authentication flows such as multi-factor login, token-based sessions, and role-based access controls further limit scanner coverage, leaving parts of the application untested.
As a result, DAST often provides coverage but not complete visibility into real-world risk.
The Business Logic Gap
Business logic vulnerabilities are flaws in how an application processes workflows, permissions, or actions. These are not coding errors but weaknesses in how the system is designed to function.
Traditional DAST tools cannot effectively detect these issues because they do not understand intent. They can confirm whether a request succeeds, but not whether it should succeed in a given situation.
For example, a user might repeat an action that should only be allowed once, or access data that belongs to another user by manipulating request flow. These vulnerabilities exist across sequences rather than single requests.
This gap explains why applications that pass security scans can still be exposed to real-world attacks.
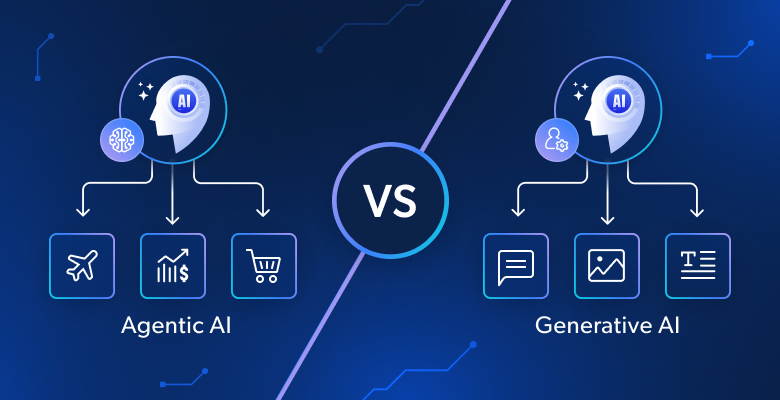
Agentic AI vs Traditional DAST
The difference between traditional DAST and agentic AI lies in how they approach testing.
DAST relies on predefined patterns and evaluates requests in isolation. It is effective for detecting known vulnerabilities but cannot adapt to complex or new scenarios.
Agentic AI takes a more adaptive approach. It analyzes how an application behaves, follows workflows across multiple steps, and adjusts its actions based on responses. Instead of stopping at detection, it explores how vulnerabilities can actually be exploited in real conditions.
This shift from static scanning to contextual reasoning makes it significantly more effective for modern applications.
From Request-Based Testing to Workflow-Level Analysis
Traditional DAST focuses on individual requests and checks whether they match known vulnerability patterns. This works for technical issues but does not reflect how real attacks occur.
Agentic AI evaluates complete workflows instead. It tracks how actions connect, how state changes over time, and how data flows between steps.
This allows it to identify vulnerabilities that only appear when multiple conditions are met, such as chained actions or bypassed workflows. These are often the highest-impact issues in modern applications.
Why Validation Matters More Than Detection
Traditional DAST tools often produce findings that require manual verification. Many of these may not be exploitable in real scenarios, which increases workload for security teams.
To address this, newer approaches focus on validating vulnerabilities rather than only detecting them. For example, ZeroThreat.ai provides an agentic AI penetration testing tool that focuses on confirming whether a vulnerability can actually be exploited within an application workflow instead of simply flagging potential issues based on patterns.
By validating exploitability, teams can reduce noise and focus on real risks. This leads to faster decision-making and more efficient remediation.
Rethinking the Role of DAST
DAST still plays an important role in application security. It is effective for identifying known vulnerabilities and maintaining baseline coverage across applications.
However, it is no longer sufficient on its own. Modern applications require testing approaches that can understand workflows, user behavior, and complex system interactions.
A stronger security strategy combines traditional scanning with more adaptive, context-aware testing methods. This ensures both known and logic-based vulnerabilities are addressed.
Conclusion
Traditional DAST remains useful for detecting known vulnerabilities, but it was not designed for the complexity of modern applications or the rise of business logic attacks.
Agentic AI introduces a more adaptive and context-aware approach that focuses on workflows, behavior, and real exploitability rather than static patterns.
For organizations, the goal is not to replace DAST but to go beyond its limitations. Combining traditional scanning with agentic AI pentesting capabilities provides a clearer understanding of real-world risk and strengthens overall application security.