Not every technical issue arrives on schedule. A staff member’s screen freezes mid-presentation. A customer cannot complete a transaction because their application has stopped responding. A remote employee’s device starts behaving in ways nobody in the office can diagnose from a phone call alone. In each of these situations, the defining factor in how quickly the problem gets resolved is not the technician’s expertise alone. It is how fast they can actually see and interact with the affected device.
Code-based attended remote support exists precisely for these moments. It is the mechanism that takes a support request from description to hands-on resolution in under a minute, without requiring any prior setup on the user’s end.
What Code-Based Support Actually Is
Attended remote support operates on a straightforward premise: the user is present, they need help, and they are willing to grant a technician temporary access to their device in order to receive it. The session code model delivers this as cleanly as possible.
When a user contacts support, the technician generates a unique, single-use session code within their platform. The user receives that code, visits a lightweight access page, enters the code, and the technician is connected. No pre-installed agent is required on the user’s machine. No account setup, no configuration, no waiting for software to download and install before help can begin.
The session exists only for the duration of that interaction. When it ends, so does all access. The user’s device cannot be reached again without a new code, a new session, and new explicit consent from the user.
Why Speed at the Start of a Support Session Matters
Every minute between a user reporting a problem and a technician beginning to work on it is a minute of disruption. For a staff member blocked from completing a task, that disruption is measurable in lost productivity. For a customer-facing team, it can translate directly into a damaged interaction with someone whose confidence in the business is already affected.
Using an attended remote support tool with session code compresses the time between “I need help” and “someone is working on it” to the shortest interval technically possible. There is no scheduling delay because no pre-installation is required. There is no back-and-forth about what software to download because the process is identical for every session. The technician generates the code, the user enters it, and the session begins.
This speed compounds across a support team’s daily volume. When first-contact resolution increases because technicians can actually see and interact with the problem rather than troubleshoot by description, the entire support operation becomes more efficient.
Trust and Consent Built Into the Workflow
One of the less discussed but genuinely important aspects of code-based attended support is what it communicates to the user. Unlike persistent remote access agents that remain on a device and can be used at any time, a session code model makes the consent transaction explicit and visible.
The user receives the code. The user enters the code. The user can see everything the technician does throughout the session. The user can end the session at any moment. When the session closes, the access is gone.
As outlined in this study, consumer and employee confidence in digital interactions is directly tied to transparency and visible control. Organizations that design their support workflows around explicit consent and observable access are better positioned to build and maintain the kind of digital trust that affects both satisfaction and long-term loyalty. Session-code-based support is one of the most practical ways to put those principles into daily operation.
The Security Dimension of Ephemeral Access
From a security standpoint, code-based attended sessions offer a meaningful advantage over models that require permanent agent installation on every supported device. Each session code is unique and time-limited. It cannot be reused, shared, or exploited after the session has ended. A support interaction with an external customer, a contractor, or a user on a personal device carries none of the ongoing access risk that a persistent remote agent would introduce.
For organizations with compliance obligations, this model is especially relevant. Many security frameworks treat access to endpoints as an event that must be authorized, documented, and bounded. As covered in this security guide, organizations should ensure that remote access to their networks is controlled, limited to what is necessary, and supported by clear endpoint security standards. A session-code model satisfies this requirement by design: access is granted only when a code is issued, only to the technician who holds that code, and only for the duration of that session.
When Code-Based Support Works Best
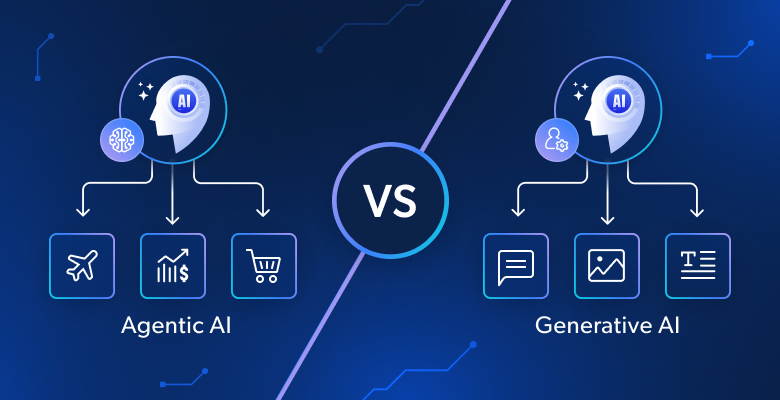
The session code model is not designed to replace every form of remote access. For regular maintenance tasks on managed devices, persistent unattended access has its own role. But for the category of support requests where a real person needs real-time help, the attended session code approach is hard to improve on.
It works equally well regardless of whether the user is an internal employee, an external customer, or a vendor contact. It requires nothing from the user’s IT environment beyond a browser and an internet connection. It scales without adding administrative overhead, because there are no agents to deploy, configure, or maintain on the user’s side.
For support teams managing a high volume of ad hoc requests, or for any organization that provides occasional technical assistance to people outside its own network, code-based attended sessions reduce every friction point between the moment help is requested and the moment the technician begins delivering it.
Frequently Asked Questions
Q1. How does a session code protect the user during a remote support interaction?
A session code is unique to a single support session and becomes invalid once that session ends. It can only be used by the technician it was generated for, and only within the time window it was created. Throughout the session, the user can see all activity on their screen and can disconnect at any moment. This structure ensures that no access persists beyond what the user explicitly authorized.
Q2. Does the user need to install software before a code-based attended session can begin?
No. One of the primary practical advantages of the session code model is that no pre-installation is required on the user’s device. The user enters the code through a lightweight access point, and the session begins without requiring them to configure, install, or maintain any software on their end. This makes it equally suitable for supporting internal staff, external customers, and users on personal or unmanaged devices.
Q3. How is attended remote support different from unattended remote access?
Attended remote support requires the user to be present and to actively participate in granting access, typically by entering a session code. Unattended remote access allows a technician to connect to a device at any time without the user being present, and requires a persistent agent to be pre-installed on the device. Both have their place in a support operation, but attended code-based sessions are specifically suited for real-time, consent-driven interactions where the user is available and actively involved in the support process.